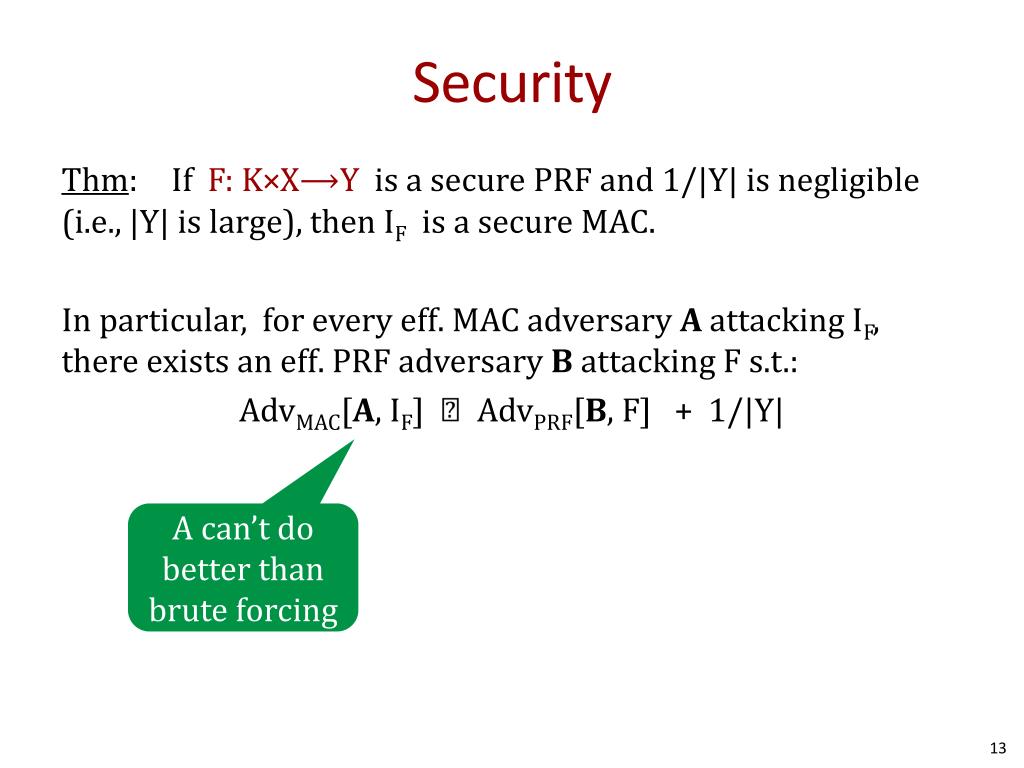
Mac Adversary Security Game
In cryptography, an adversary (rarely opponent, enemy) is a malicious entity whose aim is to prevent the users of the cryptosystem from achieving their goal (primarily privacy, integrity, and availability of data). An adversary's efforts might take the form of attempting to discover secret data, corrupting some of the data in the system, spoofing the identity of a message sender or receiver, or forcing system downtime.
Decision-Focused Learning of Adversary Behavior in Security Games Submission #20 Abstract Stackelberg security games are a critical tool for maximizing the utility of limited defense resources to protect important targets from an intelligent ad-versary. Motivated by green security, where the de-fender may only observe an adversary’s response. Game theory provides a sound mathematical approach to deploy limited security resources to maximize their effectiveness. This book distills the forefront of this research to provide the first and only study of long-term deployed applications of game theory for security for key organizations such as the Los Angeles International Airport police and the U.S. Federal Air Marshals Service.
Actual adversaries, as opposed to idealized ones, are referred to as attackers. The former term predominates in the cryptographic and the latter in the computer security literature. Eve, Mallory, Oscar and Trudy are all adversarial characters widely used in both types of texts.
This notion of an adversary helps both intuitive and formal reasoning about cryptosystems by casting security analysis of cryptosystems as a 'game' between the users and a centrally co-ordinated enemy. The notion of security of a cryptosystem is meaningful only with respect to particular attacks (usually presumed to be carried out by particular sorts of adversaries).
There are several types of adversaries depending on what capabilities or intentions they are presumed to have. Adversaries may be[1]
Start by finding your event on the MAC Football Championship 2020 2021 schedule of events with date and time listed below. We have tickets to meet every budget for the MAC Football Championship schedule. We provide world class service and premium seating. MAC Football Championship tickets from Front Row Tickets.com will make your live entertainment experience magical. Mac football championship game 2014 tickets 2016.
- computationally bounded or unbounded (i.e. in terms of time and storage resources),
- eavesdropping or Byzantine (i.e. passively listening on or actively corrupting data in the channel),
- static or adaptive (i.e. having fixed or changing behavior),
- mobile or non-mobile (e.g. in the context of network security)
Mac Adversary Security Game Board
and so on. In actual security practice, the attacks assigned to such adversaries are often seen, so such notional analysis is not merely theoretical.
How successful an adversary is at breaking a system is measured by its advantage. An adversary's advantage is the difference between the adversary's probability of breaking the system and the probability that the system can be broken by simply guessing. The advantage is specified as a function of the security parameter.
References[edit]